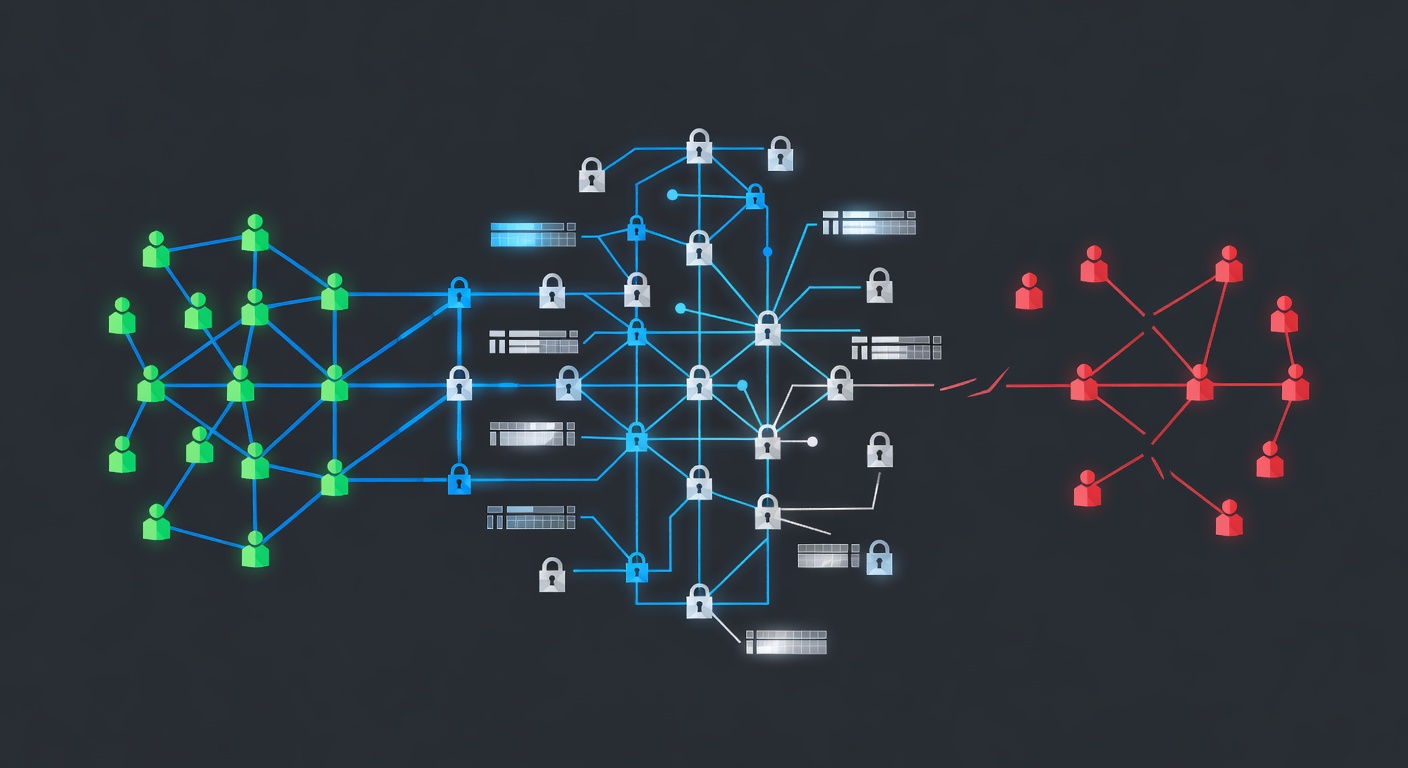
Companies spend billions on firewalls and antivirus software, but here's the uncomfortable truth—your employees are often the biggest security risk. We're breaking down why security awareness training isn't just compliance box-checking; it's your best defense against real-world attacks.
Your Team is Your Strongest (or Weakest) Link: Why Security Training Actually Matters
Your Team is Your Strongest (or Weakest) Link: Why Security Training Actually Matters
Let's be real for a second. Every day, hackers are getting smarter. Phishing emails are more convincing. Social engineering tactics are more sophisticated. And guess what? No amount of fancy technology can completely stop them.
I've seen organizations pour hundreds of thousands into enterprise-grade security systems, only to get breached because one employee clicked a suspicious link. It's frustrating, but it's also completely preventable. That's where security awareness training comes in—and it's not the boring, mandatory checkbox exercise you might think it is.
The Reality Check: Why This Matters More Than You Think
Here's the thing about cybersecurity that most people don't talk about openly: human error is the #1 cause of data breaches. Your team members are sitting at the front lines of your organization's defense, whether they realize it or not. They're the ones deciding whether to open that attachment, reuse passwords, or click a "forgot password" link that looks just a little off.
When regulations like HIPAA, PCI-DSS, and ISO 27001 started mandating security training, it wasn't because they were being overly cautious. These frameworks emerged from real incidents where inadequate security awareness led to massive data leaks and regulatory nightmares.
HIPAA: When Healthcare Gets Hacked
If you work in healthcare—or anywhere near patient data—you probably already know HIPAA is serious business. But here's what I want to highlight: HIPAA's security requirements specifically mandate ongoing staff training.
Why? Because patient data is incredibly valuable on the dark web. A single medical record can sell for more than a stolen credit card number. Healthcare providers need their teams to understand how to handle protected health information (PHI) properly, what constitutes a breach, and how to spot attacks targeting patient data.
The HIPAA Privacy Rule and Security Rule both require documented security awareness programs. This isn't optional or something you can half-ass once a year. It's a legal requirement, and auditors will check to ensure your organization is actually doing it—not just claiming to do it.
From my perspective, healthcare organizations that treat security training as a checkbox tend to end up in regulatory hot water. The ones that make it part of their culture? They're the ones staying ahead of threats.
PCI-DSS: Protecting the Money Trail
If your business touches payment card data in any way—processing, storing, or transmitting it—then PCI-DSS is your new best friend. And like HIPAA, it has serious teeth when it comes to employee training.
Payment card fraud is a $28+ billion problem globally. Hackers specifically target businesses that handle card data because the ROI is immediate and tangible. That's why PCI-DSS Goal #6 focuses heavily on security policies and staff awareness.
Here's what I find interesting: organizations compliant with PCI-DSS often see downstream benefits beyond just avoiding fines. They report:
- Better customer trust: People feel safer using their cards with companies that take security seriously
- Reduced fraud losses: Fewer breaches mean fewer chargebacks and fraud disputes
- Operational efficiency: Secure processes tend to be more streamlined processes
- Competitive advantage: You can actually market your compliance to customers and partners
When your team understands why card data is valuable and how it's targeted, they naturally become more cautious about data handling. That's the power of effective awareness training.
NIST SP 800-53: The Government Standard That Works Everywhere
NIST's 800-53 framework was created for federal agencies, but here's why I'm bringing it up: its principles are universally applicable. If you handle any sensitive or regulated data—whether it's government contracts, financial information, or intellectual property—NIST's approach is worth studying.
What makes NIST interesting is its flexibility. It's not a one-size-fits-all mandate. Instead, it provides an extensive catalog of controls that organizations can adapt to their specific risk landscape. That means your security training can be tailored to actual threats your organization faces, not generic compliance theater.
The framework pushes organizations to communicate about risk management internally. When your team understands what risks you're defending against and why certain protocols exist, compliance becomes natural behavior rather than something employees grudgingly follow.
ISO 27001 & 27002: The Global Standard
If you operate internationally or work with clients in Europe, Asia, or other regions, ISO 27001 and 27002 are probably on your radar. These standards define Information Security Management Systems (ISMS) and provide detailed controls for implementation.
What I appreciate about the ISO standards is they recognize that security is a system—not just technology, but people, processes, and policies working together. Your security training isn't separate from these standards; it's embedded throughout them.
Organizations pursuing ISO 27001 certification often discover that their training programs need significant overhauls. That's actually a good sign. It means you're moving from compliance checkbox to genuine security maturity.
The Real Talk: Training Isn't About Fear
Here's where I want to push back against conventional wisdom. A lot of security training programs are designed to scare employees. "Click this link and your company loses $1 million!" or "This mistake could get you fired!"
That approach backfires. It creates resentment, encourages employees to hide mistakes, and doesn't actually build better security habits.
Effective security awareness training should:
- Be ongoing, not annual: A single training session once a year is useless. People forget. Threats evolve. You need regular reinforcement.
- Be relevant: Generic training about "strong passwords" matters less than training about your specific threats. Is your industry targeted by ransomware? Nation-state actors? Opportunistic phishers?
- Include real examples: Employees learn better when they see actual phishing emails, social engineering attempts, and breach scenarios that could affect them.
- Make security easy: If following security protocols is painful, people will find workarounds. Your job is making secure behavior the path of least resistance.
- Measure results: Track which employees click phishing simulations, measure training completion rates, and adjust based on real data.
The Bottom Line
Security compliance isn't a punishment imposed by bureaucrats. These frameworks exist because real organizations got breached, real people had their data compromised, and regulatory bodies said "this can't happen again."
Security awareness training is your organization's immune system. Yes, you need firewalls and encryption and all the technical controls. But if your team doesn't understand security principles, your defenses are incomplete.
Whether you're dealing with HIPAA, PCI-DSS, NIST, or ISO standards, the message is consistent: invest in your people's security knowledge. It's not just about passing audits (though it helps with that). It's about genuinely reducing your risk and protecting what matters—your data, your customers, and your organization's reputation.
Start with an honest assessment: Does your team actually understand security? Not "have they completed the annual training" but do they get it? If the answer is no, that's your biggest vulnerability right there. Fix that, and everything else gets easier.
Tags: ['security-awareness-training', 'compliance-standards', 'hipaa', 'pci-dss', 'cybersecurity', 'employee-training', 'iso-27001', 'nist', 'data-protection', 'security-culture']