Small businesses think they're too insignificant to hack. They're wrong. In fact, hackers love targeting smaller companies because their defenses are usually weaker. Here's what you need to know to actually protect yourself.
Why Small Businesses Are Easy Targets (And How to Change That)
Why Small Businesses Are Easy Targets (And How to Change That)
Let me be blunt: if you run a small or medium-sized business, hackers are probably already probing your systems right now. You might not know it, but it's happening. And here's the thing that keeps me up at night—most business owners have no idea this is even a possibility.
The Uncomfortable Truth About Small Business Cybersecurity
I used to think cybersecurity was mostly a Fortune 500 problem. Big banks, tech companies, healthcare systems—sure, those are juicy targets. But then I started looking at the actual data, and it completely changed my perspective.
46% of all cyberattacks target businesses with fewer than 1,000 employees. Let that sink in. Hackers aren't snobbish about company size. In fact, they prefer smaller targets because we're easier to break into. We're the low-hanging fruit in the digital world.
Here's what really terrifies me: 60% of small businesses that get hit with a cyberattack shut down within six months. Not because of the direct financial loss alone—though that's brutal—but because of the operational chaos, customer trust destruction, and the mental toll on owners. It's a wrecking ball.
The Money Keeps Getting Worse
Let's talk numbers because they're impossible to ignore:
- A data breach now costs an average of $4.88 million—up 10% from just the year before
- The rate of attacks is accelerating faster than we can keep up. In 2023 alone, there was a 78% increase in reported data compromises compared to 2022
- Ransomware attacks jumped 13% year-over-year, and phishing attacks—the sneaky emails designed to trick you—skyrocketed by 1,265% thanks to AI-powered tricks that are getting scarily realistic
These aren't abstract numbers. These are real businesses getting destroyed.
How Hackers Actually Get In (It's Simpler Than You Think)
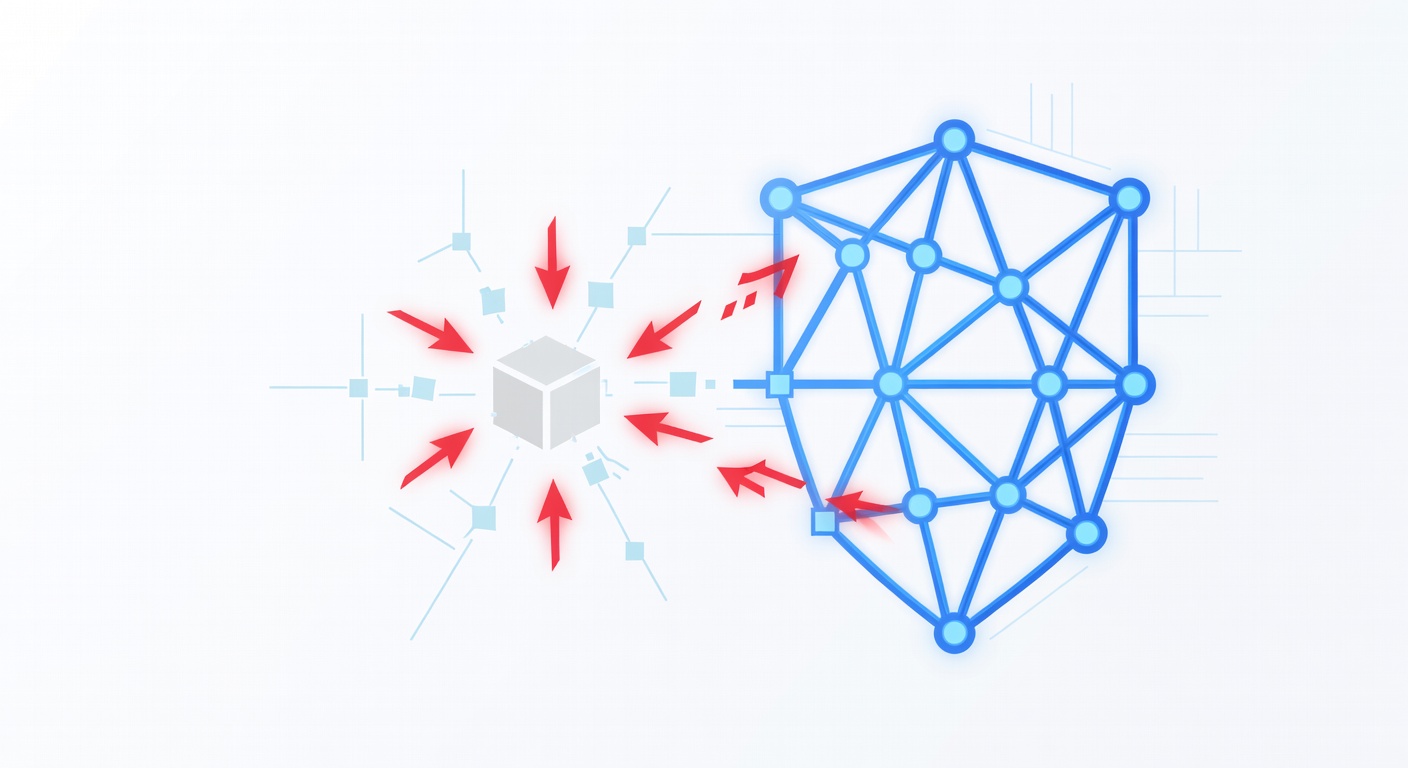
Here's what most people get wrong: hackers aren't some Hollywood villain in a dark room typing furiously at a keyboard. The attack happens in stages, and understanding them is half the battle.
Stage One: They're Watching You
Before hackers throw resources at attacking your business, they watch. They probe your systems like a burglar casing a house. They're looking for:
- Outdated software with known vulnerabilities
- Weak passwords or careless employees
- Unsecured databases
- Systems that aren't properly configured
- Employees who are susceptible to phishing emails
This reconnaissance phase is often completely silent. You won't see it happening unless you're specifically looking for it. They're gathering intel, building a mental map of your network, identifying the weakest links.
Stage Two: Building the Weapon
Once hackers understand your defenses, they craft a specific attack just for you. Maybe it's malware designed to exploit that outdated server you forgot to update. Maybe it's a convincing phishing email targeting your accounting department. Maybe it's a USB stick they plant in your parking lot hoping someone plugs it in.
This is the preparation phase, and it can take weeks or even months.
Stage Three: The Attack
Then they strike. The malware gets deployed. The phishing email gets sent. The backdoor gets installed. And here's the scary part—by the time you realize something's wrong, they might already be inside your systems.
Stage Four: The Damage
Once they're in, the damage happens fast. They encrypt your files (ransomware). They copy your sensitive data. They corrupt your backups so you can't recover. They might sit quietly, stealing data for months before you notice.
What Most Antivirus Software Gets Wrong
Here's my frustration with traditional security: it's like having a burglar alarm that goes off after someone's already in your house. It alerts you to the problem, but by then it's too late. You still have to deal with the mess.
The real problem is that traditional antivirus software is reactive. It catches some threats, sure. But it doesn't have human eyes constantly watching. It can't distinguish between a minor false alarm and the beginning of a sophisticated attack. It can't respond in real-time with the judgment and speed that experienced security professionals bring.
The Better Approach: Always-On Monitoring With Real People
What you actually need is something completely different. Think of it this way:
Instead of just an alarm, you need alarm plus a security team on standby 24 hours a day, every single day. That's the difference between hoping nothing goes wrong and actually having a defense.
A proper Managed Detection and Response (MDR) system combines:
Continuous Monitoring — Your systems are watched constantly, not just when a malware signature matches something in a database. Every network activity, login attempt, and data movement is logged and analyzed.
Smart Threat Detection — Advanced technology looks for patterns and behaviors that indicate an attack, not just known malware signatures. It catches the new stuff that hasn't been seen before.
Human Expert Analysis — Real cybersecurity professionals look at what the technology flags. They have years of experience. They know what normal looks like and what doesn't. They make judgment calls.
Immediate Response — When a threat is confirmed, it's neutralized fast. Not hours later. Now. The hackers get blocked before they can move deeper into your systems. Backups get protected. Critical data stays safe.
Containment — Even if attackers do get a foothold, they get isolated before they can spread through your network.
Why This Actually Works
The key insight is timing. If you catch an attack in the reconnaissance phase—before they even build their weapon—you win. You patch the vulnerability, block the probing, and they move on to an easier target.
If you catch them at the weaponization phase, you're still ahead.
But if you wait until they've already encrypted your data? You've lost.
An always-on MDR system catches attacks at the earliest possible stage because it's actually looking for the subtle signs that something's wrong. Not just waiting for a signature match.
What This Means For Your Business
I get it. Adding another cybersecurity service feels like just one more thing. One more expense. But here's the perspective shift: how much would it cost if you got hit? Not just in direct ransom demands or recovery costs, but in the business you'd lose? The customers who'd leave? The reputation damage?
The math actually works out. Prevention is exponentially cheaper than recovery.
And honestly? It gives you peace of mind. When you're running a business, you've got enough to worry about. Knowing that skilled professionals are actively monitoring your systems 24/7, ready to jump on any threat the moment it appears—that's genuinely valuable.
Small businesses don't have to be sitting ducks. You don't have to be that statistic that shuts down in six months. You just need to stop thinking like a small business and start protecting yourself like a business that matters—because yours does.
Tags: ['cybersecurity', 'ransomware', 'small business security', 'mdr', 'threat detection', 'data breach prevention', 'network security', 'phishing attacks', 'cyber protection']